Website Security
This article won’t make you a website security guru, but don’t underestimate the security area. The article will help you understand where threats come from, and what you can do to protect your website against the most common attacks.
We hear often about websites becoming unavailable due to DDoS attacks (Distributed Denial of Service), or strange information on a homepage and which is often damaging for yor brand.
Also the cases where millions of passwords, email addresses, and credit card details have been leaked into the public domain, exposing users to both personal embarrassment and financial risk.
Website security is all about protecting websites from unauthorized access, use, modification, destruction, or disruption – to prevent any sorts of attacks.
Effective website security requires a holistic view on the website:
- How is the website protected from unauthorized access, use, modification, destruction, or disruption?
- Does the website use a server-side web framework?
- Does the website have integrated SSL?
- Does the website have website firewall?
- Does the website have 24/7 security monitoring?
- Does the website use strong login passwords?
- Does the website use two-factor authentication for login?
- How does the website store sensitive information, e.g. last 4 digits of a credit card number?
- Does the website check and sanitize all incoming data?
Website security threats
Here is a few of the most common website threats and how they work.
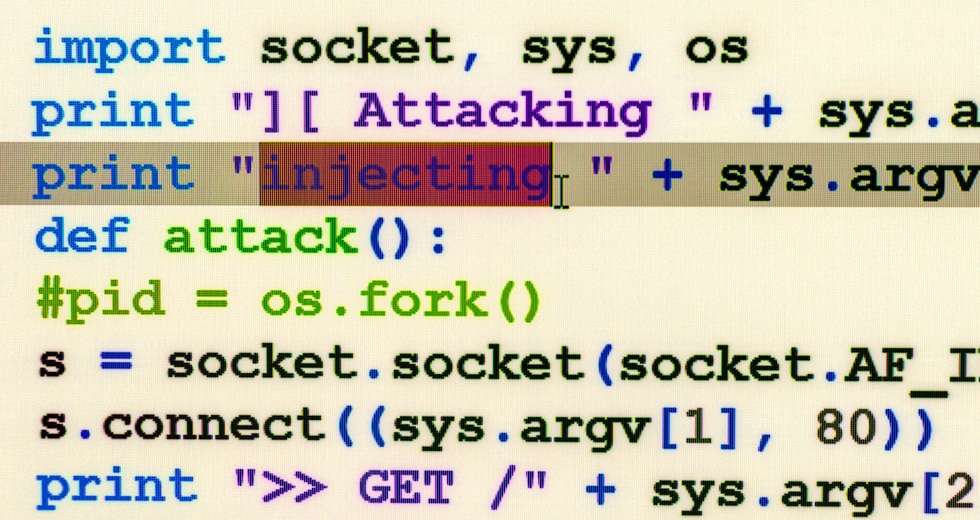
Cross-Site Scripting (XSS)
XSS vulnerabilities have been historically more common than any other type of security threat. XSS is a term used to describe a class of attacks that allow an attacker to inject client-side scripts through the website into the browsers of other users. Because the injected code comes to the browser from the site, the code is trusted and can do things like send the user’s site authorization cookie to the attacker. When the attacker has the cookie, they can log into a site as though they were the user and do anything the user can, such as access their credit card details, see contact details, or change passwords.
SQL injection
SQL injection vulnerabilities enable malicious users to execute arbitrary SQL code on a database, allowing data to be accessed, modified, or deleted irrespective of the user’s permissions. A successful injection attack might spoof identities, create new identities with administration rights, access all data on the server, or destroy/modify the data to make it unusable.
Cross-Site Request Forgery (CSRF)
CSRF attacks allow a malicious user (i.e. Jones) to execute actions using the credentials of another user without that user’s knowledge or consent. Jones knows that a particular site allows logged-in users to send money to a specified account using an HTTP POST request that includes the account name and an amount of money. Jones constructs a form that includes his bank details and an amount of money as hidden fields, and emails it to other site users – when the user clicks the submit button, an HTTP POST request will be sent to the server containing the transaction details and any client-side cookies that the browser associated with the site (adding associated site cookies to requests is normal browser behavior). The server will check the cookies, and use them to determine whether or not the user is logged in and has permission to make the transaction. The result is that any user who clicks the Submit button while they are logged in to the trading site will make the transaction. And Jones gets rich.
Clickjacking
In this attack, a malicious user hijacks clicks meant for a visible top-level site and routes them to a hidden page beneath. This technique might be used, for example, to display a legitimate bank site but capture the login credentials into an invisible “iframe” controlled by the attacker. Clickjacking could also be used to get the user to click a button on a visible site, but in doing so actually unwittingly click a completely different button. As a defense, your site can prevent itself from being embedded in an iframe in another site by setting the appropriate HTTP headers.
DDoS attacks – Distributed Denial of Service
It is an overload attack where hackers, through malware, control many computers and use them to send large amounts of requests to a website, so that the website becomes overloaded and then the access is disrupted for legitimate users. DDoS defenses usually work by identifying and blocking the “bad” traffic through the web server and allowing legitimate users through.
Directory Traversal (File and disclosure)
In this attack, a malicious user attempts to access parts of the web server file system that they should not be able to access. This vulnerability occurs when the user is able to pass filenames that include file system navigation characters (for example, ../../). The solution is to sanitize input before using it.
File Inclusion
In this attack, a user is able to specify an “unintended” file for display or execution in data passed to the server. When loaded, this file might be executed on the web server or the client-side (leading to an XSS attack). The solution is to sanitize input before using it.
Command Injection
Command injection attacks allow a malicious user to execute arbitrary system commands on the host operating system. The solution is to sanitize user input before it might be used in system calls.
Vulnerability scanner tools
Some of the best tools to scan your site for security vulnerabilities, malware, and online threats. Scanner tools that can help you find out if you’ve made any obvious mistakes.
Sucuri SiteCheck
Sucuri scanner will check the website for known malware, viruses, blacklisting status, website errors, out-of-date software, and malicious code. Sucuri also helps clean and protect your website from online threats and works on any website platform, including WordPress, Joomla, Magento, Drupal, phpBB, etc…
Mozilla Observatory
The Mozilla Observatory helpes websites by teaching developers, system administrators, and security professionals how to configure their sites safely and securely.
UpGuard
A website security scan that gives a security assessment of a website.
TermsHub
Generates a website cookie scan report. The tool also offers a free URL malware scanner and an HTTP, HTML, and SSL/TLS vulnerability scanner.
ImmuniWeb
A website security scanners that checks your site against the following standards: PCI DSS & GDPR compliance, HTTP headers, including CSP, CMS specific test for WordPress and Drupal sites and Front-end library vulnerabilities.
OWASP
OWASP provides a full list of Vulnerability Scanning Tools.
Website protection
Some simple steps you can take to protect your site:
Server-side web framework
Using a server-side web framework, will enable “by default” robust and well-thought-out defense mechanisms against a number of the more common attacks.
Secure Sockets Layer
Other attacks can be mitigated through your web server configuration by enabling HTTPS.
Website firewall
A website firewall protects your website by filtering, monitoring, and blocking any malicious HTTP/S traffic traveling to the website, and prevents any unauthorized data from leaving the site. It does this by adhering to a set of policies that help determine what traffic is malicious and what traffic is safe.
Login process
Use strong login passwords and use two-factor authentication for admin login.
WordPress
Always update WordPress, theme and plugins to the latest version.
Vulnerability scanner tools
Use vulnerability scanner tools to help you find out if you’ve made any obvious mistakes.
Don’t trust data from browser
This includes, but is not limited to data in URL parameters of GET requests, POST requests, HTTP headers and cookies, and user-uploaded files. Always check and sanitize all incoming data.